Question 41
An analyst is investigating a host in the network that appears to be communicating to a command and control server on the Internet. After collecting this packet capture the analyst cannot determine the technique and payload used for the communication.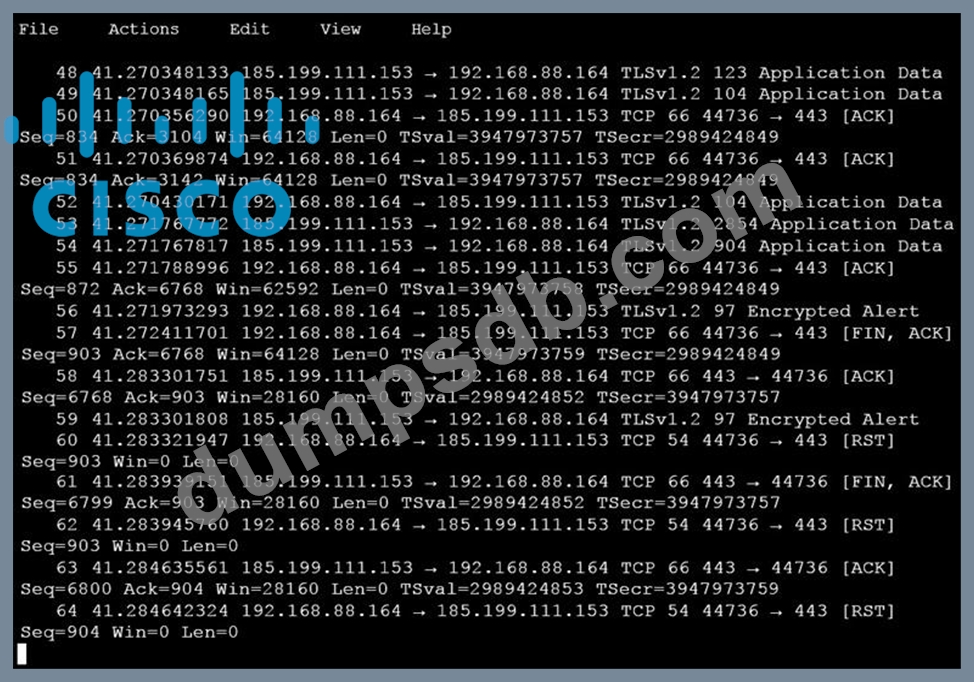
Which obfuscation technique is the attacker using?
Question 42
What describes a buffer overflow attack?
Question 43
What is a difference between inline traffic interrogation and traffic mirroring?
Question 44

An analyst is investigating a host in the network that appears to be communicating to a command and control server on the Internet. After collecting this packet capture the analyst cannot determine the technique and payload used for the communication.
Which obfuscation technique is the attacker using?
Question 45
What is a sandbox interprocess communication service?

